To secure communication, a company can use cryptography to encrypt information. Encryption involves transforming information into a non-human readable format and vice versa.
Information plays a vital role in the management of business, organizations, military operations, etc. Information in the wrong hands can lead to loss of business or catastrophic results.
In this article, we will introduce you to the world of cryptology and how you can protect information from falling into the wrong hands.
- What is encryption?
- What is cryptanalysis?
- What is encryption?
- Encryption algorithms
- Hacking Activity: Hack Now!
Encryption meaning
What does encryption mean? Cryptography is the study and application of techniques that hide the true meaning of information by transforming it into non-human readable formats and vice versa.
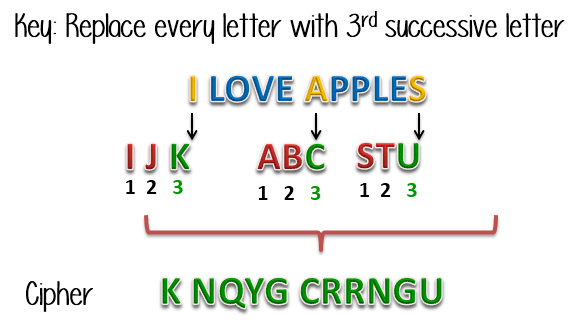
Let's illustrate this with the help of an example. Suppose you want to send the message “I LOVE MELES”, you can replace each letter of the sentence with the next third letter of the alphabet.
The encrypted message will be “K NQXG CRRNGV”. To decrypt our message, we will have to go back three letters of the alphabet using the letter we want to decrypt. The image below shows how the transformation is performed.
The process of transforming information into a non-human readable form is called encryption. The process of reversing encryption is called decryption.
Decryption is done using a secret key known only to the legitimate recipients of the information. The key is used to decrypt hidden messages.
This makes communication safe because even if the attacker gets the information, it won't make sense to him. The encrypted information is known as encryption.
What is cryptanalysis?
Cryptoanalysis is the art of attempting to decrypt encrypted messages without using the key used to encrypt the messages. Cryptoanalysis uses mathematical analysis and algorithms to decipher the digits. The success of cryptanalysis attacks depends on:
- Available time
- Computing power available
- Available memory capacity
Below is a list of commonly used Cryptanalysis attacks;
- Brute-force attack: This type of attack uses algorithms that try to guess all the possible logical combinations of the plaintext which are then encrypted and compared with the original cipher.
- Dictionary attack- This type of attack uses a list of words to match the plaintext or key. It is mainly used when trying to crack encrypted passwords.
- Rainbow table attack: This type of attack compares the ciphertext with precomputed hashes to find matches.
What is encryption?
Cryptography combines the techniques of cryptography and cryptanalysis.
Encryption algorithms
MD5 - this stands for Message-Digest 5. It is used to create 128-bit hash values. Theoretically, hashes cannot be reversed in the original plain text. MD5 is used to encrypt passwords and check data integrity. MD5 is not collision resistant. Collision resistance is the difficulty in finding two values that produce the same hash values.
- SHA: this is the acronym for Secure Hash Algorithm. SHA algorithms are used to generate condensed representations of a message (message digest). It has various versions such as;
- SHA-0: Produces 120-bit hash values. It was withdrawn from use due to significant defects and replaced by SHA-1.
- SHA-1: Produces 160-bit hash values. It is similar to previous versions of MD5. It has cryptographic weakness and is not recommended for use since the year 2010.
- SHA-2: has two hash functions, namely SHA-256 and SHA-512. SHA-256 uses 32-bit words while SHA-512 uses 64-bit words.
- SHA-3: this algorithm was formally known as Keccak.
- RC4: this algorithm is used to create stream ciphers. It is mainly used in protocols such as SSL (Secure Socket Layer) to encrypt Internet communications e WEP (Wired Equivalent Privacy) to protect wireless networks.
- BLOWFISH: This algorithm is used to create symmetrically locked and keyed ciphers. It can be used to encrypt passwords and other data.
Hacking Activity: Use CrypTool
In this practical scenario, we will create a simple code using the RC4 algorithm. We will then attempt to decrypt it using a brute force attack. For this exercise, let's assume you know that the encryption secret key is 24 bits. We will use this information to find the figure.
We will be using CrypTool 1 as our encryption tool. CrypTool 1 is an open source educational tool for cryptography studies. You can download it from https://www.cryptool.org/en/ct1-downloads
Creating the RC4 stream cipher
We will encrypt the following sentence
Never underestimate the determination of a guy who has a lot of time and little money
We will use 00 00 00 as the encryption key.
- Apri CrypTool 1
- Replace the text with Never underestimate the determination of a guy who has a lot of time and little money
- Click the Encrypt / Decrypt menu
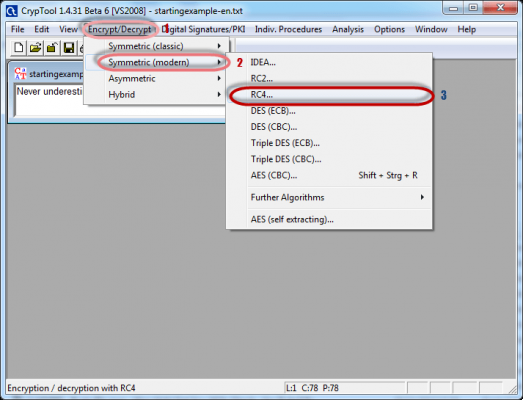
- Point to Symmetric Decryption (Modern) then select RC4 as shown above
- The following window will appear
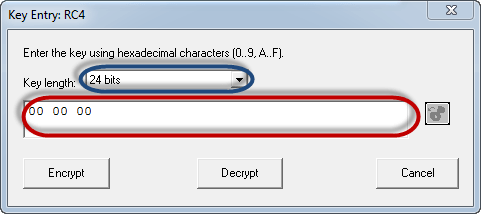
- Select 24 bits as the encryption key
- Set the value to 00 00 00
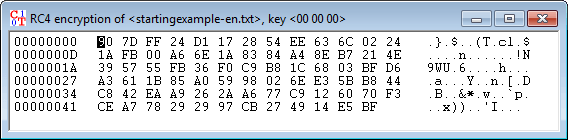
- Click the Encrypt button
- You will get the following flow code
Attacking the stream cipher
- Click the Analysis menu
- Point to Symmetric Encryption (modern) then select RC4 as shown above
- You will get the following window
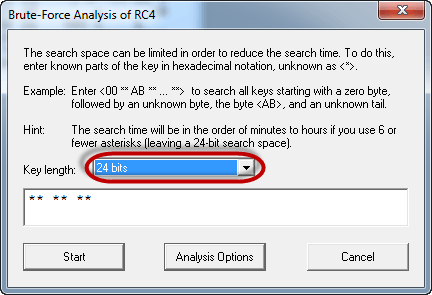
- Remember that the assumption made is that the secret key is 24 bits. So make sure you select 24 bits as the key length.
- Click the Start button. You will get the following window
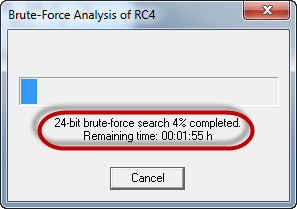
- Note: The time taken to complete the Brute-Force Analysis attack depends on the processing capacity of the machine used and the length of the key. The longer the key length, the longer it will take to complete the attack.
- When the analysis is complete, you will get the following results.
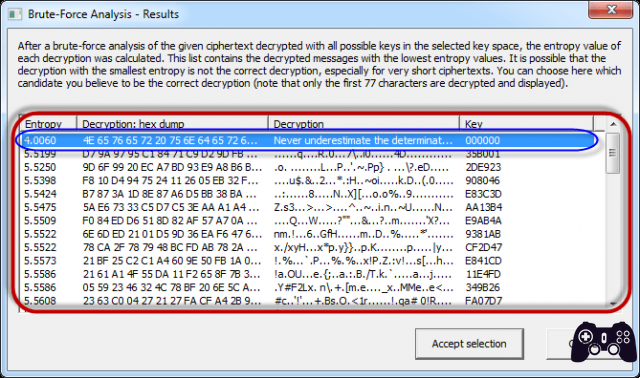
- Note: A lower entropy number means it is the most likely correct result. It is possible that an entropy value higher than the lowest found might be the correct result.
- Select the row that makes the most sense, then click the Accept Selection button when you're done
Contents
- Cryptography is the science of encrypting and decrypting messages.
- A cipher is a message that has been transformed into a non-human readable format.
- To decipher means to reverse a digit in the original text.
- Cryptoanalysis is the art of decrypting ciphers without knowing the key used to encrypt them.
- Cryptography combines the techniques of both cryptography and cryptanalyst.
It might interest you:
- How to find out passwords, various techniques
- How to hack a WiFi network
Further Reading:
- What is Google One VPN?
- What is end-to-end encryption?
- How to enable and disable end-to-end encryption in Zoom
- How to change the PIN in Bitlocker
- How to password protect a zip file and folder